Deep Security 12 FR has reached end of support. Use the version selector (above) to see more recent versions of the Help Center.
Manage and run recommendation scans
Deep Security can run recommendation scans on computers to help identify intrusion prevention, integrity monitoring, and log inspection rules that should be applied or removed.
Recommendation scans provide a good starting point for establishing a list of rules that you should implement, but there are some important additional rules that are not identified by recommendation scans. You should implement those rules manually. See Implement additional rules for common vulnerabilities
You can configure recommendation scans and implement the recommended rules for individual computers or at the policy level. For large deployments, Trend Micro recommends managing recommendations through policies. This way, you can make all your rule assignments from a single source (the policy) rather than having to manage individual rules on individual computers. This can mean that some rules are assigned to computers on which they are not required; however, the minimal effect on performance is outweighed by the ease of management that results from using policies. If you enable recommendation scans in policies, use separate policies for scanning Windows and Linux computers, to avoid assigning Windows rules to Linux computers, and vice-versa.
- What gets scanned?
- Scan limitations
- Run a recommendation scan
- Automatically implement recommendations
- Check scan results and manually assign rules
- Configure recommended rules
- Implement additional rules for common vulnerabilities
- Troubleshooting: Recommendation Scan Failure
What gets scanned?
During a recommendation scan, Deep Security Agents scan the operating system for:
- installed applications
- the Windows registry
- open ports
- the directory listing
- the file system
- running processes and services
- environment variables
- users
The Deep Security Virtual Appliance can perform agentless recommendation scans on virtual machines but only on Windows platforms and is limited to scanning the operating system for:
- installed applications
- the Windows registry
- the file system
Scan limitations
Certain technical or logical limitations result in the rules for some types of software not being accurately recommended, or not recommended at all:
- On Unix/Linux systems, the recommendation scan engine might have trouble detecting software that is not installed through the operating system's default package manager, for example, Apache Struts, Wordpress, or Joomla. Applications installed using standard package managers are not a problem.
- On Unix/Linux systems, rules for desktop application vulnerabilities or local vulnerabilities (for example, browsers and media players) are not included in recommendation scans.
- Generic web application protection rules are not included in recommendation scans.
- Smart rules are generally not included in recommendation scans unless they address a major threat or a specific vulnerability. Smart rules address one or more known and unknown (zero-day) vulnerabilities. Rule lists in Deep Security Manager identify smart rules with "Smart" in the Type column.
- When dealing with rules related to a content management system (CMS), the recommendation scan cannot detect the CMS installation and installed version. It also cannot detect the plug-ins installed with a CMS and their versions. As a result, whenever a recommendation scan finds a web server installed and PHP installed or running on a system, all CMS-related intrusion prevention rules get recommended. This may result in the over-recommendation of rules, but balances the need for security vs. accuracy.
- The recommendations for the following web technologies may suggest more rules than necessary, so some tailoring may be required:
- Red Hat JBoss
- Eclipse Jetty
- Apache Struts
- Oracle WebLogic
- WebSphere
- Oracle Application Testing Suite
- Oracle Golden Gate
- Nginx
- OpenSSL rules are recommended on Windows only when OpenSSL is explicitly installed. If OpenSSL in being used internally by an application but it was not installed as a separate package, a recommendation scan does not detect it.
- On Linux systems, rules for Java-related vulnerabilities do not get recommended if web browsers are the only applicable vector.
- Recommendation scans cannot detect the Adobe Flash Player plug-in that is included in a default Chrome installation. Recommendations are based on the Chrome version, which means some unnecessary rules may be recommended.
Run a recommendation scan
Because changes to your environment can affect which rules are recommended, it's best to run recommendation scans on a regular basis (the best practice is to perform recommendation scans on a weekly basis). Trend Micro releases new intrusion prevention rules on Tuesdays, so it's recommended that you schedule recommendation scans shortly after those releases. The use of system resources, including CPU cycles, memory, and network bandwidth, increases during a recommendation scan so it's best to schedule the scans at non-peak times.
There are several ways to run recommendation scans:
- Scheduled task: Create a scheduled task that runs recommendation scans according to a schedule that you configure. You can assign the scheduled task to all computers, one individual computer, a defined computer group, or all computers protected by a particular policy. See Create a scheduled task to regularly run recommendation scans.
- Ongoing scans: Configure a policy so that all computers protected by the policy are scanned for recommendations on a regular basis. You can also configure ongoing scans for individual computers. This type of scan checks the timestamp of the last scan that occurred and then and follows the configured interval thereafter to perform future scans. This results in recommendation scans occurring at different times in your environment. This setting is helpful in environments where an agent might not be online for more than a few days (for example, in cloud environments that are building and decommissioning instances frequently). See Configure an ongoing scan
- Manual scans: Run a single recommendation scan on one or more computers. A manual scan is useful if you’ve recently made significant platform or application changes and want to force a check for new recommendations instead of waiting for a scheduled task. See Manually run a recommendation scan.
- Command line: Initiate a recommendation scan via the Deep Security command-line interface. See Command-line basics.
- API: Initiate a recommendation scan via the Deep Security API. See Use the Deep Security API to automate tasks.
Scheduled tasks and ongoing scans are each capable of running recommendation scans independently with their own settings. Use either the scheduled tasks or ongoing scans, but not both.
Once a recommendation scan has run, alerts are raised on the all computers for which recommendations have been made.
Create a scheduled task to regularly run recommendation scans
- In the Deep Security Manager, go to the Administration > Scheduled Tasks page.
- Click New on the toolbar and select New Scheduled Task to display the New Scheduled Task wizard.
- In the Type list, select Scan Computers for Recommendations and then select how often you want the scan to occur. Click Next.
- Depending on your choice in step 3, the next page lets you be more specific about the scan frequency. Make your selection and click Next.
- Now select which computer(s) to scan and click Next.
You can select all computers, choose one individual computer, select a group of computers, or select computers that are assigned a particular policy. For large deployments, it's best to perform all actions, including recommendation scans, through policies.
- Give a name to your new scheduled task, select whether or not to Run Task on 'Finish', click Finish.
Configure an ongoing scan
- In the Deep Security Manager, open the Computer or Policy editor
 You can change these settings for a policy or for a specific computer.
To change the settings for a policy, go to the Polices page and double-click the policy that you want to edit (or select the policy and click Details).
To change the settings for a computer, go to the Computers page and double-click the computer that you want to edit (or select the computer and click Details)., depending on whether you want to configure the scan for an individual computer or for all computers that are using a policy. For large deployments, it's best to perform all actions, including recommendation scans, through policies.
You can change these settings for a policy or for a specific computer.
To change the settings for a policy, go to the Polices page and double-click the policy that you want to edit (or select the policy and click Details).
To change the settings for a computer, go to the Computers page and double-click the computer that you want to edit (or select the computer and click Details)., depending on whether you want to configure the scan for an individual computer or for all computers that are using a policy. For large deployments, it's best to perform all actions, including recommendation scans, through policies. - Click Settings. On the General tab, under Recommendations, the Perform ongoing Recommendation Scans setting enables or disables ongoing recommendation scans. The Ongoing Scan Interval setting specifies how often the scans occur. Both of those settings can be inherited from the computer or policy's parent (see Policies, inheritance, and overrides for details about how inheritance works).
Manually run a recommendation scan
- In the Deep Security Manager, go to the Computers page.
- Select the computer or computers you want to scan.
- Click Actions > Scan for Recommendations.
Cancel a recommendation scan
You can cancel a recommendation scan before it starts running.
- In the Deep Security Manager, go to the Computers page.
- Select the computer or computers where you want to cancel the scans.
- Click Actions > Cancel Recommendation Scan.
Exclude a rule or application type from recommendation scans
If you don't want a particular rule or application type to be included in recommendation scan results, you can exclude it from scans.
- In the Deep Security Manager, open the Computer or Policy editor
 You can change these settings for a policy or for a specific computer.
To change the settings for a policy, go to the Polices page and double-click the policy that you want to edit (or select the policy and click Details).
To change the settings for a computer, go to the Computers page and double-click the computer that you want to edit (or select the computer and click Details)..For large deployments, it's best to perform all actions, including recommendation scans, through policies.
You can change these settings for a policy or for a specific computer.
To change the settings for a policy, go to the Polices page and double-click the policy that you want to edit (or select the policy and click Details).
To change the settings for a computer, go to the Computers page and double-click the computer that you want to edit (or select the computer and click Details)..For large deployments, it's best to perform all actions, including recommendation scans, through policies. - Depending on which type of rule you want to exclude, go to the Intrusion Prevention, Integrity Monitoring, or Log Inspection page.
- On the General tab, click Assign/Unassign (for rules) or Application Types (for application types).
- Double-click the rule or application type that you want to exclude.
- Go to the Options tab. For rules, set Exclude from Recommendations to "Yes" or "Inherited (Yes)". For application types, select the Exclude from Recommendations checkbox.
Automatically implement recommendations
You can configure Deep Security to automatically implement recommendation scan results when it is appropriate to do so:
- In the Deep Security Manager, open the Computer or Policy editor
 You can change these settings for a policy or for a specific computer.
To change the settings for a policy, go to the Polices page and double-click the policy that you want to edit (or select the policy and click Details).
To change the settings for a computer, go to the Computers page and double-click the computer that you want to edit (or select the computer and click Details)..For large deployments, it's best to perform all actions, including recommendation scans, through policies.
You can change these settings for a policy or for a specific computer.
To change the settings for a policy, go to the Polices page and double-click the policy that you want to edit (or select the policy and click Details).
To change the settings for a computer, go to the Computers page and double-click the computer that you want to edit (or select the computer and click Details)..For large deployments, it's best to perform all actions, including recommendation scans, through policies. - Depending on which type of rules you want to implement automatically, go to the Intrusion Prevention, Integrity Monitoring, and/or Log Inspection pages. (You can change the setting independently for each protection module.)
- On the General tab, under Recommendations, change the setting to "Yes" or "Inherited (Yes)".
Not all recommendations can be implemented automatically. The exceptions are:
- Rules that require configuration before they can be applied.
- Rules that are excluded from recommendation scans.
- Rules that have been automatically assigned or unassigned but that a user has overridden. For example, if Deep Security automatically assigns a rule and you subsequently unassign it, the rule is not reassigned after the next recommendation scan.
- Rules that have been assigned at a higher level in the policy hierarchy cannot be unassigned at a lower level. A rule assigned to a computer at the policy level must be unassigned at the policy level.
- Rules that Trend Micro has issued but which may pose a risk of producing false positives. (This will be addressed in the rule description.)
Check scan results and manually assign rules
The results of the latest recommendation scan are displayed in the Computer or Policy editor![]() You can change these settings for a policy or for a specific computer.
To change the settings for a policy, go to the Polices page and double-click the policy that you want to edit (or select the policy and click Details).
To change the settings for a computer, go to the Computers page and double-click the computer that you want to edit (or select the computer and click Details)., on the General tab of the protection module (Intrusion Prevention, Integrity Monitoring, and Log Inspection).
You can change these settings for a policy or for a specific computer.
To change the settings for a policy, go to the Polices page and double-click the policy that you want to edit (or select the policy and click Details).
To change the settings for a computer, go to the Computers page and double-click the computer that you want to edit (or select the computer and click Details)., on the General tab of the protection module (Intrusion Prevention, Integrity Monitoring, and Log Inspection).
The example below describes how to deal with intrusion prevention recommendation scan results via a policy:
- Once a recommendation scan is complete, open the policy that is assigned to the computers you have just scanned.
- Go to Intrusion Prevention > General. The number of unresolved recommendations (if any) is displayed in the Recommendations section.
- Click Assign/Unassign to open the rule assignment window.
- Sort the rules By Application Type and select Recommended for Assignment from the display filter menu:
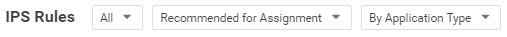
This displays a list of rules that are recommended for assignment but that have not been assigned.
- To assign a rule to the policy, select the checkbox next to the rule name. Rules flagged with a
 icon have configuration options that you can set. Rules flagged with a
icon have configuration options that you can set. Rules flagged with a  icon have settings that must be configured before the rule is enabled.)
icon have settings that must be configured before the rule is enabled.) Alternatively, to assign several rules at once, use the Shift or Control keys to select the rules, right-click the selection, and click Assign Rule(s).
 ) . A partial flag (
) . A partial flag ( ) identifies an application type where only some of the rules that are part of the application type have been recommended.
) identifies an application type where only some of the rules that are part of the application type have been recommended. Configure recommended rules
Some rules require configuration before they can be applied. For example, some log inspection rules require that you specify the location of the log files to be inspected for change. If this is the case, an alert is raised on the computer on which the recommendation has been made. The text of the alert will contain the information required to configure the rule. In the policy or computer editor, rules flagged with a  icon have configuration options that you can set. Rules flagged with a
icon have configuration options that you can set. Rules flagged with a  icon have settings that must be configured before the rule is enabled.
icon have settings that must be configured before the rule is enabled.
Implement additional rules for common vulnerabilities
Recommendation scans provide a good starting point for establishing a list of rules that you should implement, but there are some additional rules for common vulnerabilities that are not identified by recommendation scans because they need to be carefully configured and tested before being implemented in "prevent" (block) mode. Trend Micro recommends that you configure and test these rules, then manually enable them in your policies (or for individual computers):
This list includes the most common of the additional rules you should configure. You can find others in Deep Security Manager by searching for rules whose type is "Smart" or "Policy".
| Rule name | Application type |
|---|---|
| 1007598 - Identified Possible Ransomware File Rename Activity Over Network Share | DCERPC Services |
| 1007596 - Identified Possible Ransomware File Extension Rename Activity Over Network Share | DCERPC Services |
| 1006906 - Identified Usage Of PsExec Command Line Tool | DCERPC Services |
| 1007064 - Executable File Uploaded On System32 Folder Through SMB Share | DCERPC Services |
| 1003222 - Block Administrative Share | DCERPC Services |
| 1001126 - DNS Domain Blocker | DNS Client |
| 1000608 - Generic SQL Injection Prevention See Configure an SQL injection prevention rule for details. |
Web Application Common |
| 1005613 - Generic SQL Injection Prevention - 2 | Web Application Common |
| 1000552 - Generic Cross Site Scripting (XSS) Prevention | Web Application Common |
| 1006022 - Identified Suspicious Image With Embedded PHP Code | Web Application Common |
| 1005402 - Identified Suspicious User Agent In HTTP Request | Web Application Common |
| 1005934 - Identified Suspicious Command Injection Attack | Web Application Common |
| 1006823 - Identified Suspicious Command Injection Attack - 1 | Web Application Common |
| 1005933 - Identified Directory Traversal Sequence In Uri Query Parameter | Web Application Common |
| 1006067 - Identified Too Many HTTP Requests With Specific HTTP Method | Web Server Common |
| 1005434 - Disallow Upload Of A PHP File | Web Server Common |
| 1003025 - Web Server Restrict Executable File Uploads | Web Server Common |
| 1007212 - Disallow Upload Of An Archive File | Web Server Common |
| 1007213 - Disallow Upload Of A Class File | Web Server Common |
Troubleshooting: Recommendation Scan Failure
If you are receiving a Recommendation Scan Failure on your server, follow the steps below to resolve the issue. If the issue continues to persist after troubleshooting, create a diagnostic package from the agent and contact support.
Communication
Typically for communication issues "protocol error" will appear in the body of the error message.
If you don't have open inbound firewall ports from the Deep Security Manger to the agent, open the ports or switch to agent-initiated communication. For more information, see Activate and protect agents using agent-initiated activation and communication.
Server resources
Monitor the CPU and memory resources on the server. If the memory or CPU is becoming exhausted during the scan, increase the resources.
Timeout values
Increase the timeout values for the recommendation scan.
dsm_c commands are not available on Deep Security as a Service.
- Open the command prompt and navigate to the Deep Security Manager installation folder.
- Enter the commands below (if this is a multi-tenant environment, add the tenant name):
dsm_c -action changesetting -name settings.configuration.agentSocketTimeoutOverride -value 1200
dsm_c -action changesetting -name settings.configuration.defaultSocketChannelTimeout -value 1200000
dsm_c -action changesetting -name settings.configuration.recoScanKeepAliveTimeInterval -value 180000
- If you are using the Deep Security Virtual Appliance, also enter these commands:
dsm_c -action changesetting -name settings.configuration.timeoutEpsecScanRequest -value 1770
dsm_c -action changesetting -name settings.configuration.timeoutDsamCommandChannel -value 1800