Encrypt communication between the Deep Security Manager and the database
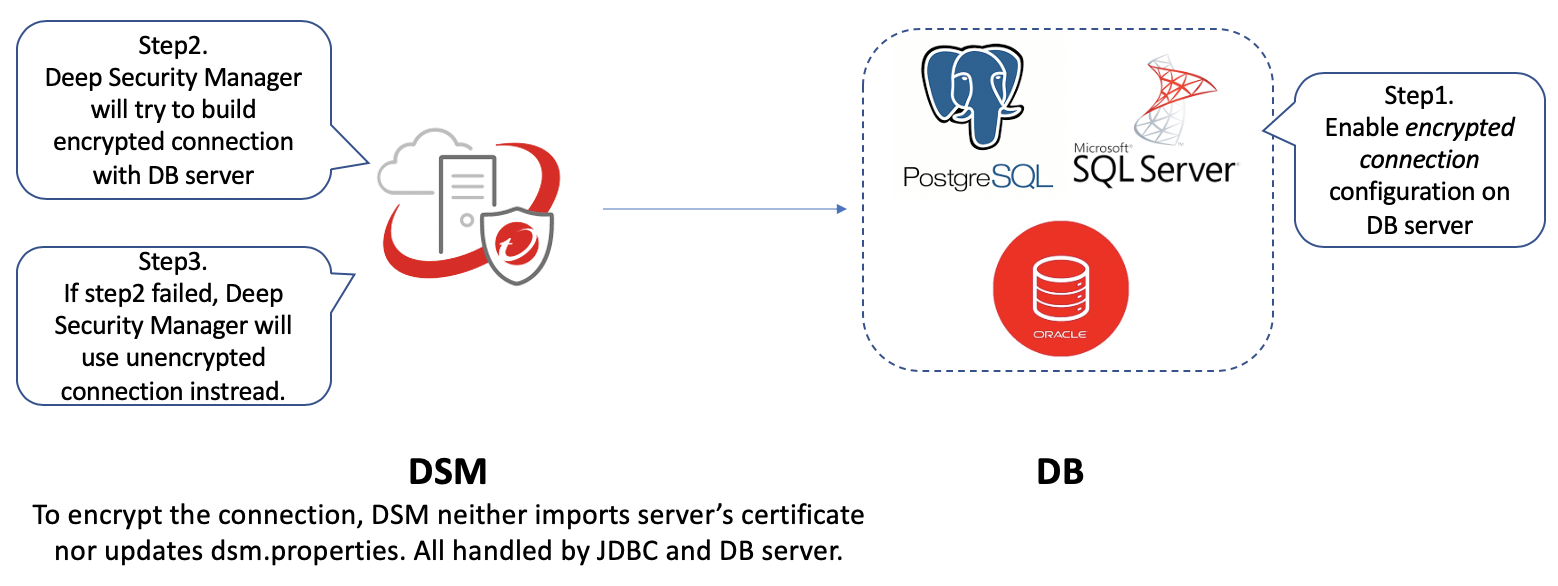
If the communication channel between the Deep Security Manager and the database is not secure, you may wish to encrypt the communications between them. In the current design, Deep Security Manager first attempts to build an encrypted connection with the database server. If it fails, Deep Security Manager uses an unencrypted connection with the database server instead.
The related mechanisms are built into the database library that Deep Security Manager is based on, therefore the server certificate doesn't need to be imported and the configuration file doesn't need to be updated. You should consult with the database vendor and their supporting documentation to determine if there will be any significant performance impact when enabling encrypted sessions.
The instructions vary depending on the database you are using:
This section also provides information on Running an agent on the database serverhow to Disable encryption between the manager and database, and how to Upgrade from an old Deep Security Manager version.
Encrypt communication between the manager and database
Microsoft SQL Server database
If you have not already installed Deep Security Manager 20:
- Follow the instructions in Enable encrypted connections to the Database Engine on the Microsoft MSDN site and enable encrypted connection options on Microsoft SQL Server.
By default, the communication between Deep Security Manager 20 and Microsoft SQL Server is encrypted.
If you have already installed Deep Security Manager 20 and you haven't enabled encryption options on your Microsoft SQL Server:
- Stop Deep Security Manager 20.
- Follow the instructions in Enable encrypted connections to the Database Engine on the Microsoft MSDN site and enable encrypted connection options on Microsoft SQL Server.
- Restart the Deep Security Manager.
By default, the communication between Deep Security Manager 20 and Microsoft SQL Server is encrypted.
select client_net_address,connect_time,net_transport,protocol_type,encrypt_option from sys.dm_exec_connections to see if your Deep Security Manager encrypted connection is working or not.Oracle database
If you have not already installed Deep Security Manager 20:
- Follow the instructions How To Configure Data Encryption and Integrity on the Oracle Help Center, and enable encrypted connection options on Oracle Database Server side.
By default, the communication between Deep Security Manager 20 and Oracle Database Server is encrypted.
If you have already installed Deep Security Manager 20 and you haven't enabled encryption options on your Oracle Database Server:
- Stop Deep Security Manager 20.
- Follow the instructions How To Configure Data Encryption and Integrity on the Oracle Help Center, and enable encrypted connection options on Oracle Database Server side.
- Restart the Deep Security Manager.
By default, the communication between Deep Security Manager 20 and Oracle Database Server is encrypted.
Follow the Oracle blog article Verifying the use of Native Encryption and Integrity to see if the encrypted connection is working or not.
PostgreSQL
If you have not already installed Deep Security Manager 20:
- Turn on SSL in PostgreSQL. For on-premises PostgreSQL database, see Secure TCP/IP Connections with SSL for more information. For an Amazon RDS for PostgreSQL, see Using SSL with a PostgreSQL DB Instance for more information.
By default, the communication between Deep Security Manager 20 and PostgreSQL Database Server is encrypted.
If you have already installed Deep Security Manager 20 and you haven't enabled encryption options on your PostgreSQL Database Server:
- Stop Deep Security Manager 20.
- Turn on SSL in PostgreSQL. For on-premises PostgreSQL database, see Secure TCP/IP Connections with SSL for more information. For an Amazon RDS for PostgreSQL, see Using SSL with a PostgreSQL DB Instance for more information.
- Restart the Deep Security Manager.
By default, the communication between Deep Security Manager 20 and PostgreSQL Database Server is encrypted.
To check that the manager is connected using TLS, use the following query and check the SSL column: select a.client_addr, a.application_name, a.usename, s.* from pg_stat_ssl s join pg_stat_activity a using (pid) where a.datname='<Deep Security database name>';
Running an agent on the database server
Encryption should be enabled if you are using an agent to protect the database. When you perform a security update, the Deep Security Manager stores new Intrusion Prevention rules in the database. The rule names themselves will almost certainly generate false positives as they get parsed by the agent if the data is not encrypted.
Disable encryption between the manager and database
In rare cases, you may need to disable encryption between Deep Security Manager and the database. For example, if you're using an older version of SQL Server, you may need to disable encryption to avoid connection errors. For details, see Error: The installer could not establish a secure connection to the database server.
Follow the instructions for your database type to disable encryption.
Microsoft SQL Server
- Stop the Deep Security Manager service.
- In the SQL Server, disable the "Force Encryption" option that was enabled in Enable encrypted connections to the Database Engine.
- (Optional) If your Deep Security Manager 20 was upgraded from Deep Security Manager 12.5 or older, remove all encryption related configurations in
dsm.properties: - Restart Microsoft SQL Server if necessary.
- Start Deep Security Manager.
database.SqlServer.encrypt=true
database.SqlServer.trustServerCertificate=true
If you upgraded from Deep Security 10.1 or a previous version, and your connection to the database uses named pipes as the transport, remove the following line instead: database.SqlServer.ssl=require
Oracle Database
- Stop the Deep Security Manager service.
- Follow How To Configure Data Encryption and Integrity to disable the connection encryption in the Oracle server.
- (Optional) If your Deep Security Manager 20 was upgraded from Deep Security Manager 12.5 or older, remove all encryption related configurations in dsm.properties:
- Restart the Oracle listener.
- Start the Deep Security Manager service.
database.Oracle.oracle.net.encryption_types_client=(AES256)
database.Oracle.oracle.net.encryption_client=REQUIRED
database.Oracle.oracle.net.crypto_checksum_types_client=(SHA1)
database.Oracle.oracle.net.crypto_checksum_client=REQUIRED
PostgreSQL
- Stop the Deep Security Manager service.
- Follow Secure TCP/IP Connections with SSL to remove ssl=on in postgresql.conf and disable the connection encryption in the PostgrSQL database.
- (Optional) If your Deep Security Manager 20 was upgraded from Deep Security Manager 12.5 or older, remove all encryption related configurations in dsm.properties:
- Restart the PostgreSQL service.
- Start the Deep Security Manager service.
database.PostgreSQL.connectionParameters=ssl=true
Upgrade from an old Deep Security Manager version
If you're currently using Deep Security Manager 12.5 or older and meet the following criteria:
- Encrypted connection is enabled.
- Uses PostgreSQL database server.
Please follow the instructions below before upgrading.
If either of the above criteria is not satisfied, you can ignore the following section and upgrade straight to Deep Security Manager 20.0.
Upgrade Deep Security Manager
Since PostgreSQL JDBC driver has different behaviors in different versions, you need to complete the following steps before upgrading.
- Export the certificate from your PostgreSQL database server. (This should already be completed because the old Deep Security Manager requires the certificate to enable connection encryption).
- Rename the certificate file as root.crt .
- Put it in the predefined Deep Security Manager 20 path:
- Run the upgrade flow. Deep Security Manager 20 will continue to use an encrypted connection with PostgreSQL server after upgrade.
In Linux, put root.crt in ~/.postgresql/
In Windows, put root.crt in c:\Users\{USERNAME}\AppData\Roaming\postgresql\.