GCP auto scaling and Deep Security
You can set up automatic protection in Deep Security for new GCP VM instances created through GCP managed instance groups (MIGs) to support auto scaling.
Each GCP VM instance created through a MIG will need to have a Deep Security agent installed on it. There are two ways that you can do this: you can include a pre-installed agent in the GCP VM instance used to create the instance template, or you can install the agent by including a deployment script in the instance template for the image. There are pros and cons for each option:
- If you include a pre-installed agent, instances will spin up more quickly because there is no need to download and install the agent software. The downside is that the agent software might not be the latest. To work around this issue, you can enable the upgrade on activation feature.
- If you use a deployment script to install the agent, it will always get the latest version of the agent software from the Deep Security Manager.
Pre-install the agent
If you have a GCP VM instance already configured with a Deep Security Agent, you can use that instance to create the instance template for the MIG. Before creating the instance template, you must deactivate the agent on the GCP VM instance and stop the instance:
dsa_control -r
Each new GCP VM instance created by the MIG needs to have its agent activated and a policy applied to it, if it doesn’t have one already. There are two ways to do this:
- You can create a deployment script that activates the agent and optionally applies a policy. Then add the deployment script to the GCP instance template so that it is run when a new instance is created. For instructions, see the Install the agent with a deployment script section below, but omit the section of the deployment script that gets and installs the agent. You will only need the dsa_control -a section of the script.
For the deployment scripts to work, agent-initiated communication must be enabled on your Deep Security Manager. For details on this setting, see Activate and protect agents using agent-initiated activation and communication.
- You can set up an event-based task in Deep Security Manager that will activate the agent and optionally apply a policy when an instance is launched and the "Computer Created (By System)" event occurs.
Install the agent with a deployment script
Deep Security provides the ability to generate customized deployment scripts that you can run when GCP VM instances are created. If the GCP VM instance does not contain a pre-installed agent, the deployment script should install the agent, activate it, apply a policy, and optionally assign the machine to a computer group and relay group.
You can generate deployment scripts to automate the agent installation using the Deep Security API. For more information, see Generate an agent deployment script.
In order for the deployment script to work:
- You must create images from machines that are stopped.
- Agent-initiated communication must be enabled on your Deep Security Manager. For details on this setting, see Activate and protect agents using agent-initiated activation and communication.
To set up automatic protection for instances using a deployment script:
- Sign in to Deep Security Manager.
- From the Support menu in the top right-hand corner, select Deployment Scripts.
- Select your platform.
- Select Activate Agent automatically after installation.
- Select the appropriate Security Policy, Computer Group and Relay Group.
- Click Copy to Clipboard.
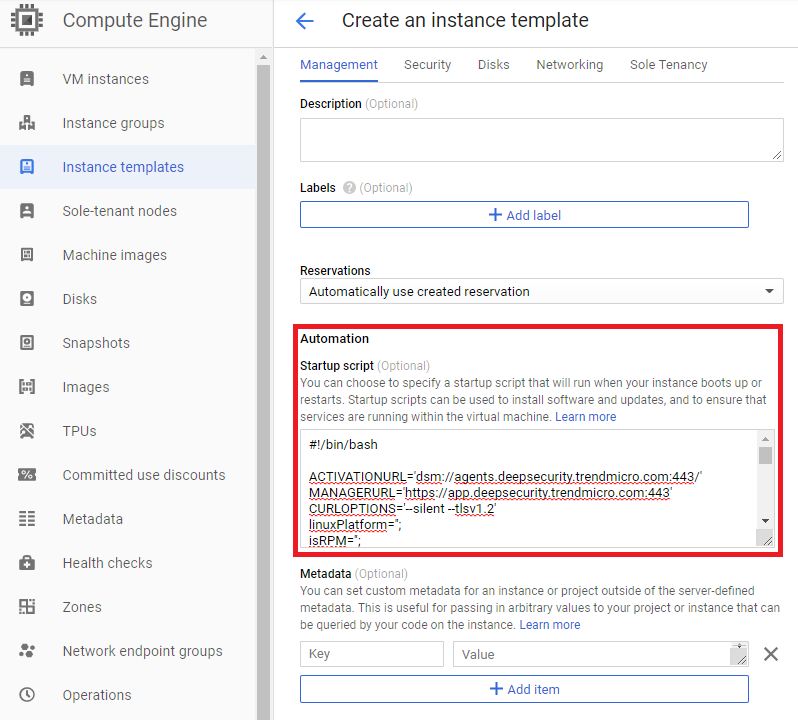
- Go to the GCP instance templates, expand Management, security, disks, networking, sole tenancy and paste the deployment script into Startup script.
Delete instances from Deep Security as a result of GCP MIGs
After you have added a GCP account in Deep Security Manager, instances that no longer exist in GCP as a result of Managed Instance Group will be automatically removed from the Deep Security Manager.
See Add a Google Cloud Platform account for details on adding a GCP account.