Deep Security 12 FR has reached end of support. Use the version selector (above) to see more recent versions of the Help Center.
Define roles for users
Deep Security uses role-based access control (RBAC) to restrict user permissions to parts of Deep Security. Access rights and editing privileges are attached to roles and not to users. Once you have installed Deep Security Manager, you should create individual accounts for each user and assign each user a role that will restrict their activities to all but those necessary for the completion of their duties. To change the access rights and editing privileges of an individual user, you must assign a different role to the user or edit the role.
The access that roles have to computers and policies can be restricted to subsets of computers and policies. For example, users can be permitted to view all existing computers, but only permitted to modify those in a particular group.
Deep Security comes preconfigured with two roles:
- Full Access: The full access role grants the user all possible privileges in terms of managing the Deep Security system including creating, editing, and deleting computers, computer groups, policies, rules, malware scan configurations, and others.
- Auditor: The auditor role gives the user the ability to view all the information in the Deep Security system but without the ability to make any modifications except to their own personal settings, such as password, contact information, dashboard layout preferences, and others.
You can create new roles that can restrict users from editing or even seeing Deep Security objects such as specific computers, the properties of security rules, or the system settings.
Before creating user accounts, identify the roles that your users will take and itemize what Deep Security objects those roles will require access to and what the nature of that access will be (viewing, editing, creating, and so on). Once you have created your roles, you can then begin creating user accounts and assigning them specific roles.
Clicking New ( ) or Properties (
) or Properties ( ) displays the Role properties window with six tabs (General, Computer Rights, Policy Rights, User Rights, Other Rights, and Assigned To).
) displays the Role properties window with six tabs (General, Computer Rights, Policy Rights, User Rights, Other Rights, and Assigned To).
Add or edit a role
- In Deep Security Manager go to Administration > User Management > Roles.
- Click New to add a new role or double-click an existing role to edits its settings.
- Specify the general properties for the role, including:
- Name: The name of the role, which will appear on the Roles page and in the list of available roles when adding a user.
- Description: (Optional) A description of the role.
- Access Type: Select whether users with this role will have access to Deep Security Manager, the Deep Security Manager Web service API (applies to the legacy SOAP and REST APIs), or both.
-
To enable the legacy SOAP and REST Web service APIs, go to Administration > System Settings > Advanced > SOAP Web Service API.
-
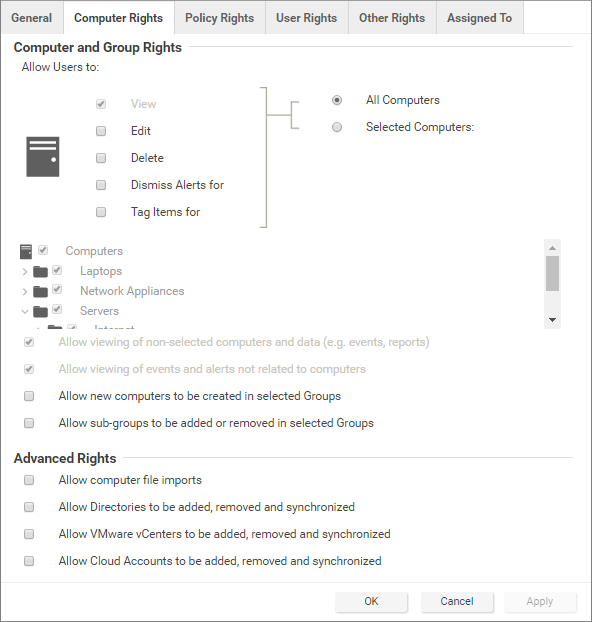
Use the Computer Rights pane to confer viewing, editing, deleting, alert-dismissal, and event tagging rights to users in a role. These rights can apply to all computers and computer groups or they can be restricted to only certain computers. If you wish to restrict access, select the Selected Computers radio button and put a check next to the computer groups and computers that users in this role will have access to.
-
These rights restrictions will affect not only the user's access to computers in Deep Security Manager, but also what information is visible, including events and alerts. As well, email notifications will only be sent if they relate to data that the user has access rights to.
 Four basic options are available:
Four basic options are available:- Allow viewing of non-selected computers and data: If users in this role have restricted edit, delete, or dismiss-alerts rights, you can still allow them to view but not change information about other computers by checking this box.
- Allow viewing of events and alerts not related to computers: Set this option to allow users in this role to view non-computer-related information (for example, system events, like users being locked out, new firewall rules being created, IP Lists being deleted, and so on)
The previous two settings affect the data that users have access to. Although the ability of a user to make changes to computers have been restricted, these two settings control whether they can see information relating to computers they don't otherwise have access to. This includes receiving email notifications related to those computers.
- Allow new computers to be created in selected Groups: Set this option to allow users in this role to create new computers in the computer groups they have access to.
- Allow sub-groups to be added/removed in selected Groups: Set this option to allow users in this role to create and delete subgroups within the computer groups they have access to.
You can also enabled these in the Advanced Rights section:
- Allow computer file imports: Allow Users in this Role to import computers using files created using the Deep Security Manager's Computer Export option.
- Allow Directories to be added, removed and synchronized: Allow Users in this Role to add, remove, and synchronize computers that are being managed using an LDAP-based directory like MS Active Directory. (Not available with Deep Security as a Service)
- Allow VMware vCenters to be added, removed and synchronized: Allow Users in this Role to add, remove and synchronize VMware vCenters. (Not available with Deep Security as a Service)
- Allow Cloud Providers to be added, removed, and synchronized: Allow Users in this Role to add, remove, and synchronize Cloud Providers.
- Use the Policy Rights tab to confer viewing, editing, and deleting rights to users in a role. These rights can apply to all policies or they can be restricted to only certain policies. If you wish to restrict access, click Selected Policies and put a check mark next to the policies that users in this role will have access to.
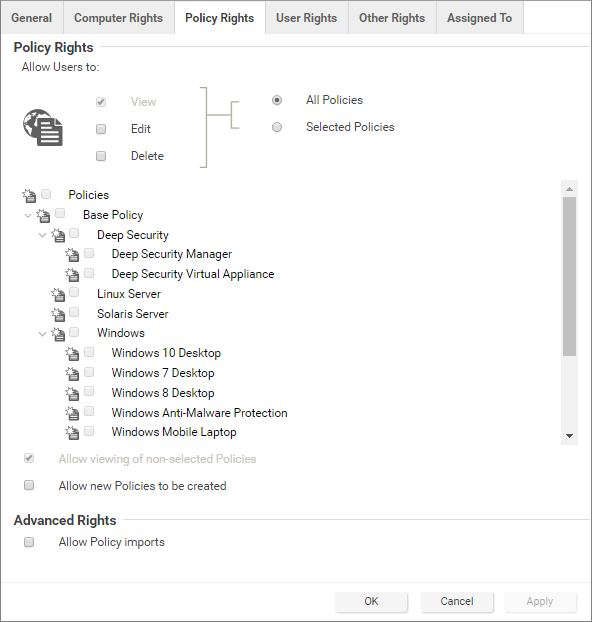 When you allow rights to a policy that has "child" policies, users automatically get rights to the child policies as well.
When you allow rights to a policy that has "child" policies, users automatically get rights to the child policies as well. Two basic options are available:
- Allow viewing of non-selected Policies: If users in this role have restricted edit or delete rights, you can still allow them to view but not change information about other policies by checking this box.
- Allow new Policies to be created: Set this option to allow users in this role to create new policies.
You can also enabled this in the Advanced Rights section:
- Allow Policy imports: Allow users in this role to import policies using files created with the Deep Security Manager Export option on the Policies tab.
- The options on the User Rights tab allow you to define permissions for administrator accounts.
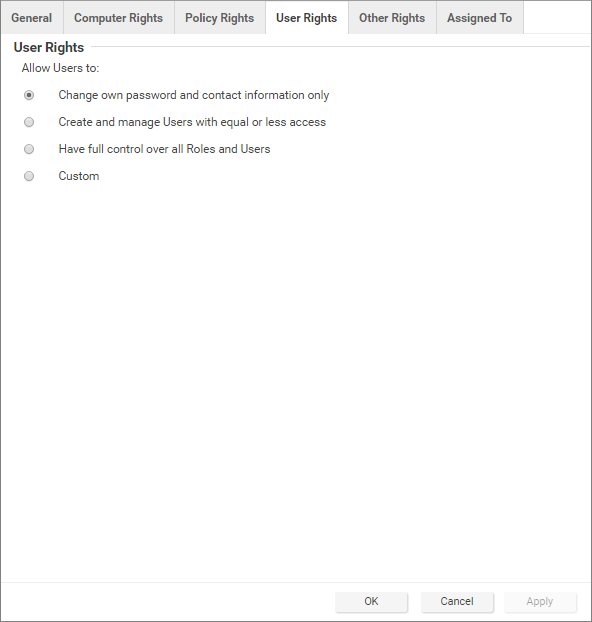
- Change own password and contact information only: Users in this role can change their own password and contact information only.
- Create and manage Users with equal or less access: Users in this role can create and manage any users who do not have any privileges greater than theirs. If there is even a single privilege that exceeds those of the users with this role, the users with this role will not be able to create or manage them.
- Have full control over all Roles and Users: Gives users in this role the ability to create and edit and users or roles without restrictions. Be careful when using this option. If you assign it to a role, you may give a user with otherwise restricted privileges the ability to create and then sign in as a user with full unrestricted access to all aspects of the Deep Security Manager.
- Custom:
You can further restrict the ability of a user to view, create, edit, or delete users and roles by selecting Custom and using the options in the Custom Rights section. Some options may be restricted for certain users if the Can only manipulate Users with equal or lesser rights option is selected.
The Can only manipulate Users with equal or lesser rights option limits the authority of users in this role. They will only be able to effect changes to users that have equal or lesser rights than themselves. Users in this Role will not be able to create, edit, or delete roles. Selecting this option also places restrictions on some of the options in the Custom Rights section:
- Can Create New Users: Can only create users with equal or lesser rights.
- Can Edit User Properties: Can only edit a user (or set or reset password) with equal or lesser rights.
- Can Delete Users: Can only delete users with equal or lesser rights.
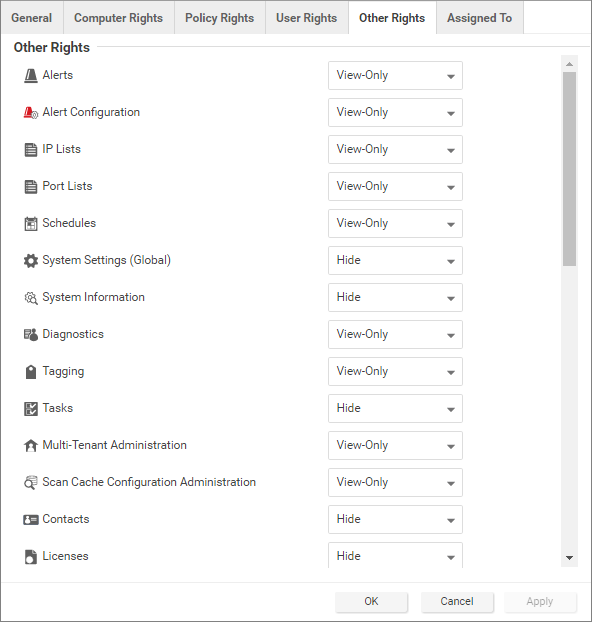
- The Other Rights tab enables you to restrict roles' permissions so that they can only access specific Deep Security features, and sometimes specific actions with those features. This can be useful if, for example, you have a team of administrators, and you want to make sure that they don't accidentally overwrite each others' work. By default, roles are View Only or Hide for each feature. To allow to full control or customized access, select Custom from the list.
- The Assigned To tab displays a list of the users who have been assigned this role. If you want to test that roles are working correctly, sign in as a newly created user and verify the functionality.
Default settings for full access, auditor, and new roles
The following table identifies the default rights settings for the full access role and the auditor role. Also listed are the rights settings that are in place when creating a new role by clicking New in the toolbar on the Roles page.
| RIGHTS | SETTINGS BY ROLE | ||
| General | Full Access Role | Auditor Role | New Role Defaults |
| Access to DSM User Interface | Allowed | Allowed | Allowed |
| Access to Web Service API | Allowed | Allowed | Not allowed |
| Computer Rights | Full Access Role | Auditor Role | New Role Defaults |
| View | Allowed, All Computers | Allowed, All Computers | Allowed, All Computers |
| Edit | Allowed, All Computers | Not allowed, All Computers | Not allowed, All Computers |
| Delete | Allowed, All Computers | Not allowed, All Computers | Not allowed, All Computers |
| Dismiss Alerts for | Allowed, All Computers | Not allowed, All Computers | Not allowed, All Computers |
| Tag Items for | Allowed, All Computers | Not allowed, All Computers | Not allowed, All Computers |
| Allow viewing of non-selected computers and data (e.g. events, reports) | Allowed | Allowed | Allowed, All Computers |
| Allow viewing of events and alerts not related to computers | Allowed | Allowed | Allowed, All Computers |
| Allow new computers to be created in selected Groups | Allowed | Not allowed | Not allowed |
| Allow sub-groups to be added or removed in selected Groups | Allowed | Not allowed | Not allowed |
| Allow computer file imports | Allowed | Not allowed | Not allowed |
| Allow Cloud Accounts to be added, removed and synchronized | Allowed | Not allowed | Not allowed |
| Policy Rights | Full Access Role | Auditor Role | New Role Defaults |
| View | Allowed, All Policies | Allowed, All Policies | Allowed, All Policies |
| Edit | Allowed, All Policies | Not allowed, All Policies | Not allowed, All Policies |
| Delete | Allowed, All Policies | Not allowed, All Policies | Not allowed, All Policies |
| View non-selected Policies | Allowed | Allowed | Allowed |
| Create new Policies | Allowed | Not allowed | Not allowed |
| Import Policies | Allowed | Not allowed | Not allowed |
| User Rights (See note on User rights below) | Full Access Role | Auditor Role | New Role Defaults |
| View Users | Allowed | Allowed | Not allowed |
| Create Users | Allowed | Not allowed | Not allowed |
| Edit User Properties | Allowed | Not allowed | Not allowed |
| Delete Users | Allowed | Not allowed | Not allowed |
| View Roles | Allowed | Allowed | Not allowed |
| Create Roles | Allowed | Not allowed | Not allowed |
| Edit Role Properties | Allowed | Not allowed | Not allowed |
| Delete Roles | Allowed | Not allowed | Not allowed |
| Delegate Authority | Allowed | Not allowed | Not allowed |
| Other Rights | Full Access Role | Auditor Role | New Role Defaults |
| Alerts | Full (Can Dismiss Global Alerts) | View-Only | View-Only |
| Alert Configuration | Full (Can Edit Alert Configurations) | View-Only | View-Only |
| IP Lists | Full (Can Create, Edit, Delete) | View-Only | View-Only |
| Port Lists | Full (Can Create, Edit, Delete) | View-Only | View-Only |
| Schedules | Full (Can Create, Edit, Delete) | View-Only | View-Only |
| System Settings (Global) | Full (Can View, Edit System Settings (Global)) | View-Only | Hide |
| Diagnostics | Full (Can Create Diagnostic Packages) | View-Only | View-Only |
| Tagging | Full (Can Tag (Items not belonging to Computers), Can Delete Tags, Can Update Non-Owned Auto-Tag Rules, Can Run Non-Owned Auto-Tag Rules, Can Delete Non-Owned Auto-Tag Rules) | View-Only | View-Only |
| Tasks | Full (Can View, Add, Edit, Delete Tasks, Execute Tasks) | View-Only | Hide |
| Multi-Tenant Administration | Full | Hide | View-Only |
| Scan Cache Configuration Administration | Full | View-Only | View-Only |
| Contacts | Full (Can View, Create, Edit, Delete Contacts) | View-Only | Hide |
| Licenses | Full (Can View, Change License) | View-Only | Hide |
| Updates | Full (Can Add, Edit, Delete Software; Can View Update For Components; Can Download, Import, Apply Update Components; Can Delete Deep Security Rule Updates) | View-Only | Hide |
| Asset Values | Full (Can Create, Edit, Delete Asset Values) | View-Only | View-Only |
| Certificates | Full (Can Create, Delete SSL Certificates) | View-Only | View-Only |
| Relay Groups | Full | View-Only | View-Only |
| Proxy | Full | View-Only | View-Only |
| SAML Identity Providers | Full | Hide | Hide |
| Malware Scan Configuration | Full (Can Create, Edit, Delete Malware Scan Configuration) | View-Only | View-Only |
| Quarantined File | Full (Can Delete, Download Quarantined File) | View-Only | View-Only |
| Web Reputation Configuration | Full | View-Only | View-Only |
| Directory Lists | Full (Can Create, Edit, Delete) | View-Only | View-Only |
| File Lists | Full (Can Create, Edit, Delete) | View-Only | View-Only |
| File Extension Lists | Full (Can Create, Edit, Delete) | View-Only | View-Only |
| Firewall Rules | Full (Can Create, Edit, Delete Firewall Rules) | View-Only | View-Only |
| Firewall Stateful Configurations | Full (Can Create, Edit, Delete Firewall Stateful Configurations) | View-Only | View-Only |
| Intrusion Prevention Rules | Full (Can Create, Edit, Delete) | View-Only | View-Only |
| Application Types | Full (Can Create, Edit, Delete) | View-Only | View-Only |
| MAC Lists | Full (Can Create, Edit, Delete) | View-Only | View-Only |
| Contexts | Full (Can Create, Edit, Delete) | View-Only | View-Only |
| Integrity Monitoring Rules | Full (Can Create, Edit, Delete) | View-Only | View-Only |
| Log Inspection Rules | Full (Can Create, Edit, Delete) | View-Only | View-Only |
| Log Inspection Decoders | Full (Can Create, Edit, Delete) | View-Only | View-Only |
| Application Control Rulesets | Full (Can Create, View, Edit, or Delete Application Control rulesets) | Hide | Hide |
| Application Control Rule | Full (Can Create, View, Edit, or Delete Application Control rules) | Hide | Hide |
| Application Control Unrecognized Software | Full (Can View or Allow/Block unrecognized software) | Hide | Hide |
| Application Control Software Inventory | Full (Can Create, View, or Delete software inventory) | Hide | Hide |
The custom settings corresponding to the Change own password and contact information only option are listed in the following table:
| Custom settings corresponding to "Change own password and contact information only" option | |
| Users | |
| Can View Users | Not allowed |
| Can Create New Users | Not allowed |
| Can Edit User Properties (User can always edit select properties of own account) | Not allowed |
| Can Delete Users | Not allowed |
| Roles | |
| Can View Roles | Not allowed |
| Can Create New Roles | Not allowed |
| Can Edit Role Properties (Warning: conferring this right will let Users with this Role edit their own rights) | Not allowed |
| Can Delete Roles | Not allowed |
| Delegate Authority | |
| Can only manipulate Users with equal or lesser rights | Not allowed |
The custom settings corresponding to the Create and manage Users with equal or less access option are listed in the following table:
| Custom settings corresponding to "Create and manage Users with equal or less access" option | |
| Users | |
| Can View Users | Allowed |
| Can Create New Users | Allowed |
| Can Edit User Properties (User can always edit select properties of own account) | Allowed |
| Can Delete Users | Allowed |
| Roles | |
| Can View Roles | Not allowed |
| Can Create New Roles | Not allowed |
| Can Edit Role Properties (Warning: conferring this right will let Users with this Role edit their own rights) | Not allowed |
| Can Delete Roles | Not allowed |
| Delegate Authority | |
| Can only manipulate Users with equal or lesser rights | Allowed |
The custom settings corresponding to the Have full control over all Roles and Users option are listed in the following table:
| Custom settings corresponding to "Have full control over all Roles and Users" option | |
| Users | |
| Can View Users | Allowed |
| Can Create New Users | Allowed |
| Can Edit User Properties (User can always edit select properties of own account) | Allowed |
| Can Delete Users | Allowed |
| Roles | |
| Can View Roles | Allowed |
| Can Create New Roles | Allowed |
| Can Edit Role Properties (Warning: conferring this right will let Users with this Role edit their own rights) | Allowed |
| Can Delete Roles | Allowed |
| Delegate Authority | |
| Can only manipulate Users with equal or lesser rights | Not applicable |