Linux Secure Boot support for agents
When Linux Secure Boot is enabled on a Deep Security Agent computer, the Linux kernel performs a signature check on kernel modules before they are installed. These Deep Security features install kernel modules:
- Anti-Malware
- Web Reputation
- Firewall
- Integrity Monitoring
- Intrusion Prevention
- Application Control
The Deep Security Agent is only compatible with Secure Boot on RHEL 7.
If you intend to use any of those modules on a Linux computer where Secure Boot is enabled, you must enroll the Trend Micro public keys for RHEL 7 (see Download a Trend Micro public key) into the Linux computer's firmware so that it recognizes the Trend Micro kernel module's signature. Otherwise, the kernel module can't be installed.
Deep Security refreshes the kernel module signing key in every major release (for example, 10.0 and 11.0). To keep security features functioning when you upgrade a Deep Security Agent to a new major release, you must enroll the new public key into any Linux computers that have Secure Boot enabled. You may see "Engine Offline" error message in the Deep Security Manager console because the operating system will not load the upgraded kernel module until the new public key is enrolled.
If you are protecting VMware virtual machines, the Secure Boot feature is available for VMware vSphere 6.5 or newer. For instructions on how to enable it, see Enable or Disable UEFI Secure Boot for a Virtual Machine on the VMware Docs site.
The Secure Boot feature is not available for AWS instances and Azure VMs.
Download a Trend Micro public key
You can download Trend Micro public keys from the list below:
If you have trouble downloading the following files, right-click and select Save Link As.
-
This public key for Deep Security Agent 11 will expire on December 5, 2022. To continue using the agent after this date, you must enroll the new DS11_2022.der Secure Boot key with a SHA1 hash of 0d 0b 3b ff ee 28 fa df 30 80 e9 bb 88 63 d0 57 fe 07 47 af.
Enroll a key using Shim MOK Manager Key Database
To enroll the Trend Micro public keys:
- On the RHEL 7 computer that you want to protect, install the Deep Security Agent, if it isn't installed already.
- Install the Machine Owner Key (MOK) facility, if it isn't already installed:
yum install mokutil
- Add the public keys to the MOK list:
mokutil --import /opt/ds_agent/DS12.der /opt/ds_agent/DS11.der
For the mokutil --import command to work, its paths need to match the location of your keys. The command above is adding keys from /opt/ds_agent/.
For details about manually adding the public key to the MOK list, see your Linux documentation.
- When prompted, enter a password that you will use later in this procedure.
- Reboot the system.
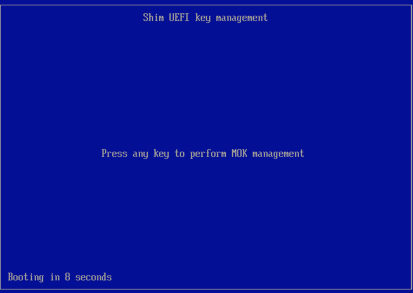
- After the computer restarts, the Shim UEFI key management console opens:
- Press any key to get started.
- On the Perform MOK management screen, select Enroll MOK.
- On the Enroll MOK screen, select View key 0.
- On the Enroll the key(s)? screen, select Yes and then enter the password you set in Step 4, above.
- On the The system must now be rebooted screen, select OK to confirm your changes and reboot.
- Use the mokutil utility to check if the key successfully enrolled or not:
- Install the keyctl utility, if it isn't already installed:
yum install keyutils
- Use the keyctl utility to list the keys that are on the system key ring:
keyctl list %:.system_keyring
You should see the Trend Micro signing key listed.
mokutil --test-key /opt/ds_agent/DS12.der
mokutil --test-key /opt/ds_agent/DS11.der
For the mokutil --test-key command to work, its path needs to match the location of your key. The commands above are testing keys from /opt/ds_agent/.