Deep Security 11 has reached end of support. Use the version selector (above) to see more recent versions of the Help Center.
Automate offline computer removal with inactive agent cleanup
If your Deep Security deployment has a large number of offline computers not communicating with the Deep Security Manager, first try using a connector (see Add AWS cloud accounts or Add a Microsoft Azure account to Deep Security). When you use a connector, the complete life cycle of your computers is managed automatically, meaning that computers deleted from your cloud accounts are also automatically removed from Deep Security. If you can't use a connector in your environment, you can automate the removal of inactive computers using inactive agent cleanup. Inactive agent cleanup will check hourly for computers that have been offline and inactive for a specified period of time (from 2 weeks to 12 months) and remove them.
Inactive agent cleanup will remove a maximum of 1000 offline computers at each hourly check. If there are more offline computers than this, 1000 will be removed at each consecutive check until all of the offline computers have been removed.
After enabling inactive agent cleanup, you can also
- Ensure computers that are offline for extended periods of time remain protected with Deep Security (optional but recommended).
- Set an override to prevent specific computers from being removed (optional).
- Check the audit trail for computers removed by an inactive cleanup job.
Inactive agent cleanup does not remove offline computers that have been added by a cloud connector.
Enable inactive agent cleanup
- Go to the Administration page.
- Under System Settings > Agents > Inactive Agent Cleanup, select Delete Agents that have been inactive for.
- From the list, select the period that a computer must be inactive before being removed.
- Ensure computers that are offline for extended periods of time remain protected with Deep Security (optional but recommended).
- Click Save.
Ensure computers that are offline for extended periods of time remain protected with Deep Security
If you have offline computers that are active but communicate irregularly with the Deep Security Manager, inactive agent cleanup will remove them if they don't communicate within the period of inactivity you defined. To ensure that these computers reconnect to Deep Security Manager, we recommend enabling both Agent-Initiated Activation and Reactivate unknown Agents. To do so, under System Settings > Agents > Agent Initiated Activation, first select Allow Agent-Initiated Activation and then select Reactivate Unknown Agents.
When a removed computer reconnects, it will not have a policy, and will be added as a new computer. Any direct links to the computer will be removed from the Deep Security Manager event data.
You can automatically assign a policy assigned to a computer upon agent-initiated activation with an event-based task.
Set an override to prevent specific computers from being removed
You can set an override at the computer or policy level to explicitly prevent computers from being removed by inactive agent cleanup.
To set an override
- Open the Computer or Policy editor
 You can change these settings for a policy or for a specific computer.
To change the settings for a policy, go to the Polices page and double-click the policy that you want to edit (or select the policy and click Details).
To change the settings for a computer, go to the Computers page and double-click the computer that you want to edit (or select the computer and click Details). for the computer or policy you want to set an override on.
You can change these settings for a policy or for a specific computer.
To change the settings for a policy, go to the Polices page and double-click the policy that you want to edit (or select the policy and click Details).
To change the settings for a computer, go to the Computers page and double-click the computer that you want to edit (or select the computer and click Details). for the computer or policy you want to set an override on. - Go to Settings > General.
- Under Inactive Agent Cleanup Override, select Yes.
- Click Save.
Check the audit trail for computers removed by an inactive cleanup job
When an inactive agent cleanup job runs, system events will be generated that you can use to track removed computers.
You'll need to check the following system events:
- 2953 - Inactive Agent Cleanup Completed Successfully
- 251 - Computer Deleted
- 716 - Reactivation Attempted by Unknown Agent (if 'Reactivate Unknown Agents' is enabled)
Search system events
To view the system events generated by an inactive agent cleanup job, you need to create a search that filters for them:
- Go to the Events and Reports page.
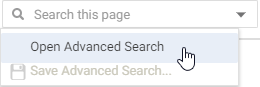
- In the top-right corner, click the Search field list and select Open Advanced Search.
- For the Period, select Custom Range from the list.
- For From, enter the date and time just before the inactive agent cleanup job was first run. For To, enter the date and time just after the cleanup job finished.
- For the Search, select Event ID and In, and then enter 2953, 251. You can optionally enter 716 and any of the event IDs (130, 790, 350, 250) associated with computer reactivation.
This will display all the system events generated by an inactive agent cleanup job. You can sort the events by time, event ID or event name by clicking on the corresponding column. You can then double-click an event to get more information about it, as detailed below.
System event details
2953 - Inactive Agent Cleanup Completed Successfully
This event is generated when the inactive agent cleanup job runs and successfully removes computers. The description for this event will tell you how many computers were removed.
If more than one check is needed to remove all computers, a separate system event will be generated for each check.
251 - Computer Deleted
In addition to the 'Inactive Agent Cleanup Completed Successfully' event, a separate 'Computer Deleted' event is generated for each computer that was removed.
716 - Reactivation Attempted by Unknown Agent
If Reactivate Unknown Agents is enabled, this event will be generated for an activated computer that was removed when it attempts to reconnect to the Deep Security Manager. Each reactivated computer will also generate the following system events:
- 130 - Credentials Generated
- 790 - Agent-Initiated Activation Requested
- 350 - Policy Created (if you've enabled an event-based task that assigns a policy)
- 250 - Computer Created
or
252 - Computer Updated