Deep Security Manager 10 has reached end of support. Use the version selector (above) to see more recent versions of the Help Center.
Integrity monitoring events
This article covers how to access and work with integrity monitoring events. For general best practices related to events, see Events in Deep Security.
To see the integrity monitoring events captured by Deep Security, go to Events & Reports > Events > Integrity Monitoring Events.
What information is displayed for integrity monitoring events?
These columns can be displayed on the Integrity Monitoring Events page. You can click Columns to select which columns are displayed in the table.
- Time: Time the event took place on the computer.
- Computer: The computer on which this event was logged. (If the computer has been removed, this entry will read "Unknown Computer".)
- Reason: The integrity monitoring rule associated with this event.
- Tag(s): Event tags that are applied to this event.
- Change: The change detected by the integrity rule. Can be: Created, Updated, Deleted, or Renamed.
- Rank: The ranking system provides a way to quantify the importance of events. By assigning "asset values" to computers, and assigning "severity values" to rules, the importance ("rank") of an event is calculated by multiplying the two values together. This allows you to sort events by rank.
- Severity: The integrity monitoring rule's severity value
- Type: Type of entity from which the event originated
- Key: Path and file name or registry key from which the event originated
- User: User ID of the file owner
- Process: Process from which the event originated
- Event Origin: The Deep Security component from which the event originated
See details about an event
Double-clicking an event (or right-clicking an event and clicking View) displays a window that contains additional information about the event. The Tags tab displays tags that have been attached to this event. For more information on event tagging, see Apply tags to identify and group events.
You can also right-click an event and select Computer Details to open the Computer editor for the computer that generated the event.
To view the properties of the rule associated with an event, right-click the event and select Integrity Monitoring Rule Properties.
Find a particular event
You can use the lists at the top of each events page to filter and group the events. Select the values that you want to filter for and then click the large blue arrow on the right side to apply the filter. You can also use the search bar in the upper-right corner to search for a specific event.
To perform an advanced search, click the arrow in the Search bar and select Open Advanced Search.
The Period setting lets you filter the list to display only those events that occurred within a specific time-frame.
The Computers setting lets you organize the display of event log entries by computer groups or policies.
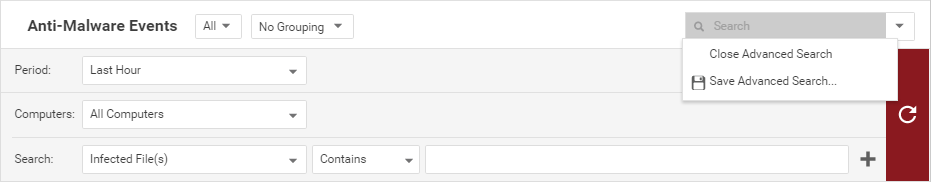
Advanced Search functions (searches are not case sensitive):
- Contains: The entry in the selected column contains the search string
- Does Not Contain: The entry in the selected column does not contain the search string
- Equals: The entry in the selected column exactly matches the search string
- Does Not Equal: The entry in the selected column does not exactly match the search string
- In: The entry in the selected column exactly matches one of the comma-separated search string entries
- Not In: The entry in the selected column does not exactly match any of the comma-separated search string entries
Pressing the "plus" button (+) to the right of the search bar will display an additional search bar so you can apply multiple parameters to your search. When your search parameters are ready, click the large blue arrow on the right side.
Export a list of events
Clicking Export exports all or selected events to a CSV file.
Tag events
Clicking Auto-Tagging displays a list of existing auto-tagging rules that have been applied to the events. You can also right-click an event to manually add or remove tags. (See Apply tags to identify and group events.)