Deep Security 11.2 has reached end of support. Use the version selector (above) to see more recent versions of the Help Center.
View and change application control rulesets
Each computer has its own application control ruleset. You can:
- View application control rulesets and find out which rules they include.
When you first enable application control for a computer, the software installed on the computer is added to the computer's inventory and allowed to run. However, you cannot see the rules associated with the inventory from Deep Security Manager unless you use the Deep Security API to do so (see Use the API to create shared and global rulesets ). In Deep Security Manager, a computer's ruleset appears empty until you create some allow/block rules for the computer.
- Change the action for an application control rule if a software file should no longer be allowed/blocked.
- Delete an individual application control rule if the software has been removed and isn't likely to return.
- Delete an application control ruleset if the computer associated with the ruleset has been removed.
If a user reports that application control is blocking software that they need to run on a particular computer, you can undo the block rule on that computer. Go to Events & Reports > Application Control Events > Security Events, find the computer, locate the block event, and then click View Rules. In the pop-up that appears, you can change the block rule to an allow rule.
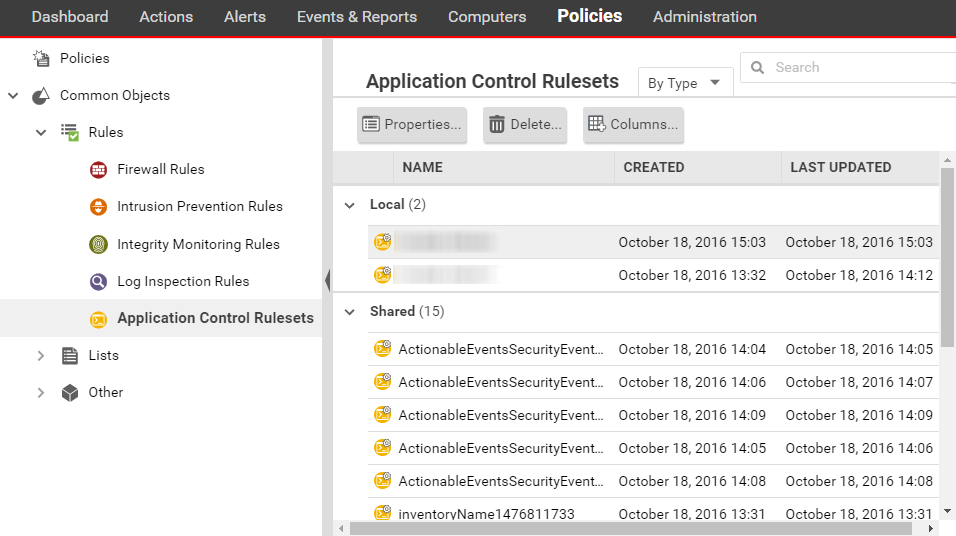
View application control rulesets
To view the list of application control rulesets, go to Policies > Common Objects > Rules > Application Control Rulesets.
To see which rules are part of a ruleset, double-click the ruleset and go to the Rules tab. The Rules tab displays the software files that have rules associated with them and enables you to change allow rules to block, and vice versa. (See Change the action for an application control rule.)
Security Events
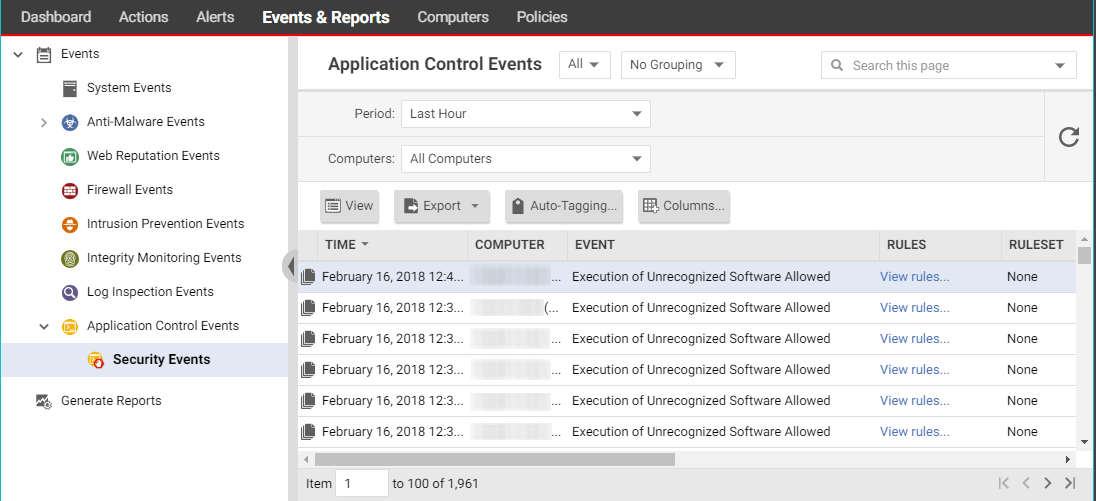
Events & Reports > Events > Application Control Events > Security Events displays all unrecognized software that either has been run on a computer or has been actively blocked from running. You can filter this list by time period and other criteria.
For each event (except aggregated events), you can click View rules to change the rule from Allow to Block or vice versa.
Deep Security Agent 10.2 or later includes event aggregation logic to reduce the volume of logs when the same event occurs repeatedly. (See Interpret aggregated security events.)
Change the action for an application control rule
If you want to allow a software that you previously blocked (or the opposite), you can edit the action in the rule. If you need to undo the rule so that the software is not recognized by application control (in other words, delete the rule, not only change its action), see Delete an individual application control rule instead.
- Go to Policies > Common Objects > Rules > Application Control Rulesets.
-
Double-click to select the ruleset that contains the rule that you want to change.
- On the pop-up window that appears, go to the Rules tab.
-
If you want to focus on software that was blocked (or allowed), then in the menu next to Application Control Rules, select By Action or By Path to group similar rules. Alternatively, you can use the search to filter the list.
If you want to change the action for a software file, but it has multiple different file names or paths, select By File Name or By Path to group related rules.
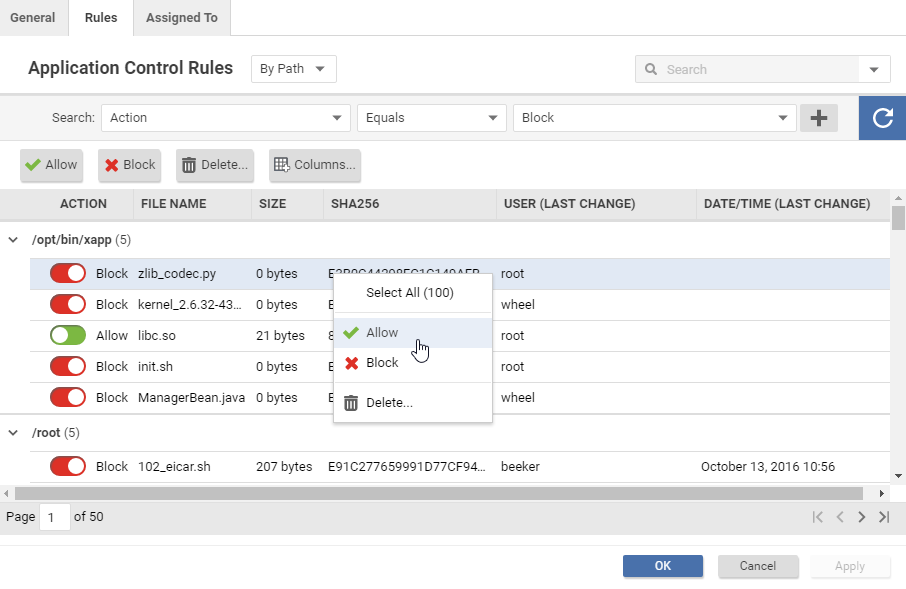
- Find the row for the specific software that you want to allow or block.
-
In the Action column, change the setting to allow or block, then click OK.
The next time that the agent connects with Deep Security Manager, the rule will be updated, and the version number will increase.
Delete an individual application control rule
If you want to undo a rule that you created, go to Policies > Common Objects > Rules > Application Control Rulesets, double-click the ruleset that contains the rule, go to the Rules tab, select the rule and then click Delete.
Some things to keep in mind:
- When the rules are not needed anymore, you can delete them to reduce the size of the ruleset. This improves performance by reducing RAM and CPU usage.
- If you delete a rule, application control will not recognize the software anymore. If the software is installed again, it will appear again on the Actions tab.
- If a software update is unstable and you might need to downgrade, keep rules that allow rollback to the previous software version until you have completed testing.
- To find the oldest rules, go to Policies > Rules > Application Control Rulesets, then click Columns. Select Date/Time (Last Change), click OK, and then click that column's header to sort by date.
Delete an application control ruleset
If an application control ruleset is not being used anymore (for example, if the computer associated with the ruleset no longer exists), you can delete it.
To delete a ruleset, go to Policies > Rules > Application Control Rulesets, click a ruleset to select it, and click Delete.