Deep Security 10.3 has reached end of support. Use the version selector (above) to see more recent versions of the Help Center.
View and restore identified malware
An identified file is a file that has been found to be or to contain malware and has therefore been encrypted and moved to a special folder. (See the "Quarantine" action in Customize malware remedial actions.) Whether or not an infected file is quarantined depends on the anti-malware configuration that was in effect when the file was scanned.
- See a list of identified files
- Working with identified files
- Search for an identified file
- Restore quarantined files
- Manually restore quarantined files
For information about events that are generated when malware is encountered, see Anti-malware events.
See a list of identified files
The Events and Reports page provides a list of identified files. From there you can see the details for any of those files.
- Click Events & Reports > Events > Anti-Malware Events > Identified Files.
- To see the details of a file, select the file and click View.
The list of identified files includes the following columns of information:
- Infected File: Shows the name of the infected file and the specific security risk.
- Malware: Names the malware infection.
- Computer: Indicates the name of the computer with the suspected infection.
The Details window provides the following information:
- Detection Time: The date and time on the infected computer that the infection was detected.
- Infected File(s): The name of the infected file.
- File SHA-1: The SHA-1 hash of the file.
- Malware: The name of the malware that was found.
- Scan Type: Indicates whether the malware was detected by a Real-time, Scheduled, or Manual scan.
- Action Taken: The result of the action taken by Deep Security when the malware was detected.
- Computer: The computer on which this file was found. (If the computer has been removed, this entry will read "Unknown Computer".)
- Container Name: Name of the Docker container where the malware was found.
- Container ID: ID of the Docker container where the malware was found.
- Container Image Name: Image name of the Docker container where the malware was found.
Working with identified files
The Identified Files page allows you to manage tasks related to identified files. Using the menu bar or the right-click context menu, you can:
- Restore
 Restore only quarantined files back to their original location and condition.
Restore only quarantined files back to their original location and condition. - Download
 Move identified files from the computer
or Virtual Appliance to a location of your choice.
Move identified files from the computer
or Virtual Appliance to a location of your choice. - Analyze
 Analyze identified files from the computer
or Virtual Appliance to a location of your choice.
Analyze identified files from the computer
or Virtual Appliance to a location of your choice. - Delete
 Delete one or more identified files from the computer
or Virtual Appliance.
Delete one or more identified files from the computer
or Virtual Appliance. - Export
 information about the identified file(s) (not the file itself) to a CSV file.
information about the identified file(s) (not the file itself) to a CSV file. - View the details (
 ) of a an identified file.
) of a an identified file. - View the Computer Details (
 ) screen of the computer on which the malware was detected.
) screen of the computer on which the malware was detected. - View Anti-Malware Event
 displays the Anti-Malware event associated with this identified file.
displays the Anti-Malware event associated with this identified file. - Add or Remove Columns
 columns can be added or removed by clicking Add/Remove.
columns can be added or removed by clicking Add/Remove. - Search
 for a particular identified file.
for a particular identified file.
- When a VM is moved to another ESXi host by vMotion, identified files associated with that VM will be deleted from the Virtual Appliance.
- When a VM is deactivated from the Deep Security Manager, identified files associated with that VM will be deleted from the Virtual Appliance.
- When a Virtual Appliance is deactivated from the Deep Security Manager, all the identified files stored on that Virtual Appliance will be deleted.
- When a Virtual Appliance is deleted from the vCenter, all the identified files stored on that Virtual Appliance will also be deleted.
Search for an identified file
- Use the Period drop down menu to see only the files that were identified within a specific time frame.
- Use the Computers drop-down menu to organize files by Computer Groups or Computer Policies.
- Click Search this page > Open Advanced Search to toggle the display of the advanced search options:
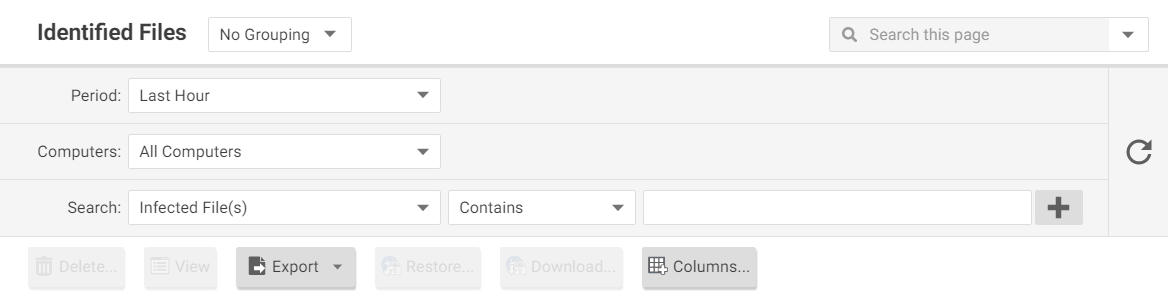
Advanced searches include one or more search criteria for filtering identified files. Each criterion is a logical statement comprised of the following items:
- The characteristic of the identified file to filter on, such as the type of file (infected file or malware) or the computer that was affected.
- An operator:
- Contains: The entry in the selected column contains the search string.
- Does Not Contain: The entry in the selected column does not contain the search string.
- Equals: The entry in the selected column exactly matches the search string.
- Does Not Equal: The entry in the selected column does not exactly match the search string.
- In: The entry in the selected column exactly matches one of the comma-separated search string entries.
- Not In: The entry in the selected column does not exactly match any of the comma-separated search string entries.
- A value.
To add a criterion, click the "plus" button (+) to the right of the topmost criterion.To search, click the Search button (the circular arrow).
Restore quarantined files
To restore quarantined files, perform the following tasks:
Create a scan exclusion for the file
Before you can restore the file to its original location you have to create a scan exclusion so that Deep Security doesn't immediately re-quarantine the file when it reappears on the computer.
- Open the Computers page and go to Anti-Malware > Identified Files and double click the quarantined file to view its properties.
- Note the file's exact name and original location.
- Still in the Computers page, go to Anti-Malware > General and click the Edit button next to each Malware Scan that's in effect to open the Malware Scan Configuration properties window.
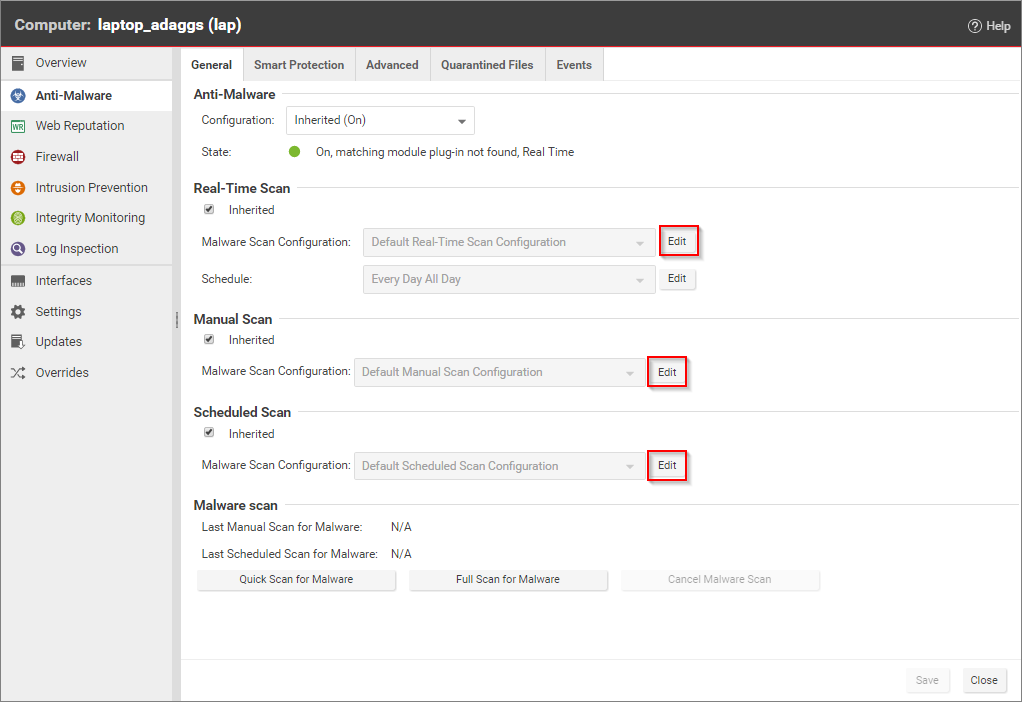
- In the Malware Scan Configuration properties window, click on the Exclusions tab.
- In the Scan Exclusions area, select File List and then either press edit if a file list is already selected, or select New from the menu to create a new File List.
- In the File List properties window, enter the file path and name of the file to be restored. Click OK to close the File List properties window.
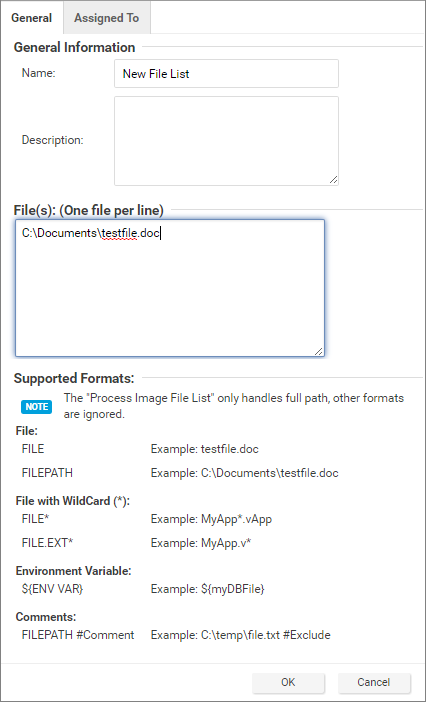
- Close the Malware Scan Configuration properties window by clicking OK.
- When you've edited all the Malware Scan Configurations, click Save in the Computers page to save your changes. You're now ready to restore your file.
Restore the file
- Still in the Computers page, go to the Anti-Malware > Identified Files tab.
- Right-click the quarantined file and select Actions > Restore and follow the steps in the wizard.
Your file will be restored to its original location.
Manually restore quarantined files
To manually restore a quarantined file, download the file to your computer. The Identified File wizard will display a link to an Administration Utility which you can use to decrypt, examine, or restore the file. Use the quarantined file decryption utility to decrypt the file and then move it back to its original location.
The decryption utility is in a zip file, QFAdminUtil_win32.zip, located in the "util" folder under the Deep Security Manager root directory. The zipped file contains two utilities which perform the same function: QDecrypt.exe and QDecrypt.com. Running QDecrypt.exe invokes an open file dialog that lets you select the file for decryption. QDecrypt.com is a command-line utility with the following options:
- /h, --help: show this help message
- --verbose: generate verbose log messages
- /i, --in=<str>: quarantined file to be decrypted, where <str> is the name of the quarantined file
- /o, --out=<str>: decrypted file output, where <str> is the name given to the resulting decrypted file